The number of online attacks increases and weak passwords is one of the main reasons. Learn how to create stronger passwords and be safer online.
Passwords are probably the most sensible aspect of our lives today. With more and more leaks happening every day, it's strongly recommended to start thinking about stronger passwords for our personal online accounts and our applications. So how can we leverage existing tools in a non-complex way to enhance our online protection?
Let's take a look.
What you should do
Let's start with simple basic tips for everyone. For starters, this is what we should be doing:- Using passwords with at least 8 characters;
- Using complex passwords that include numbers, symbols, and punctuation;
- Using a variety of passwords for different accounts or roles;
- Using a secure password tool;
What you should not do
It's also important to remember what we should not do. For example, below I list somethings we should not be doing:- using dictionary words as passwords, e.g. apple, cat, Raptors, etc;
- use sequences of characters, e.g. 3333, abcdabcd;
- use personal information in passwords, e.g. your birthdate;
- reutilize passwords;
- avoid setting the password as the associated service, e.g. Gm@il or Dropbox123;
- combinations of those above;
Other interesting tips to increase our protection are:
- Avoid storing passwords on devices that you take out of home;
- Use a password manager to securely keep track of your passwords (see the section below);
- Setup MFA/2FA when available (see the section below);
- Use a secure password generator to generate stronger passwords (see the section below);
- Never remember a password!
Use Password Managers
While the above tips are good to start and have in mind, let's now see concrete examples in how we can increase the complexity of our passwords and how we can protect them from external access. Utilizing stronger password demands a better memory. In case you don't have one as me, I strongly recommend the utilization of a password manager like 1password, KeePass and it's forks KeePassX and KeePassXC. That's why I never remember my passwords! =)
And because I need to access my passwords on Linux and Windows machines, I'm currently using KeePassXC. I also advocate for files on disk instead of services like LastPass because you cannot trust anyone else nowadays =). How safe is LastPass data for example? Well, they were hacked before...
Using KeePass
Since KeePass is one of the most familiar out there, let's provide a very quick introduction on it. The rest, I'm pretty sure you can figure out. Also, if you're using one of its forks, should be the same, just varying the visual look and feel.
Step 1 - Create your password database
The first step is to create your password database. Launch KeePass,
Step 2 - Start adding your passwords
See? KeePass not only manages our passwords but also helps us generating a very complex passwords for us.
Step 3 - Keep using it!
Yes, keep using it! Add all your accounts to this file and keep it safe on your disk, doing periodical backups. And sice KeePass is remembering your passwords for you, you have no excuses for sharing passwords or using simple passwords. Plus, backing up this file online is safer as the file is encrypted and assuming you didn't choose a very simple password for the file, it should take a long time for someone to crack it.
Which takes us to the next tip...
Which takes us to the next tip...
Recycle Passwords
Another relevant tip is recycling passwords. You may have already figured out that it's a technical term for not reusing the same passwords. But why? Yes, you should recycle your passwords every 3 months or so. It helps against data leaks. Or, if your service has something like a password expiration policy, even better:
 |
| Source: Outlook.com |
How to create stronger Passwords
Most password managers have a very useful tool to generate passwords. After getting familiar with KeePass, I suggest getting acquainted with the Password generation tool. To access it, do:
MFA adds a very strong security component to our online accounts since it reduces dramatically the chances an unauthorized user can access our accounts. Many recent hacks such as the celebrity hack could have been avoided if MFA was enabled. But Apple have learned from the episode and now advise users to protect themselves using 2FA:
Then you choose one of the options below to get your code:
Just access that type and enter your password to get a quick feedback on how long it would take for someone to crack your passwords:
Tools -> Password Generator:
As we can there there are lots of intresting options here:
- You can set the length of the generated passwords;
- You can set/unset multiple options (I would recommend checking at least 4 of them);
- You can provide patterns, certain characters;
- You can strengthen entropy by clicking on the "Advanced" button
And, by clicking on the "Generate" button, KeePass will generate a password for you. It will even tell you how strong your password is (92 bits in this case). Remember to keep an eye on the bar. It will tip you how strong your password is. In theory, we should have the tool generate passwords for us as their algorithm handles better the complexity required.
Enable multiple-factor authentication
Multiple-Factor Authentication (MFA) and it's simpler form Two-Factor Authentication (2FA) is a way of logging in that requires more then a password. Example: a text message or a verification e-mail with a random code on a different email account are sent and the user will only be allowed access if she enters the right code..MFA adds a very strong security component to our online accounts since it reduces dramatically the chances an unauthorized user can access our accounts. Many recent hacks such as the celebrity hack could have been avoided if MFA was enabled. But Apple have learned from the episode and now advise users to protect themselves using 2FA:
To protect against this type of attack, we advise all users to always use a strong password and enable two-step verification. Both of these are addressed on our website at http://support.apple.com/kb/ht4232.
Example 1 - Enabling MFA for an Apple ID
The majority of the most used websites currently offer MFA. As an example, here's what you need to do to enable MFA on you Apple ID.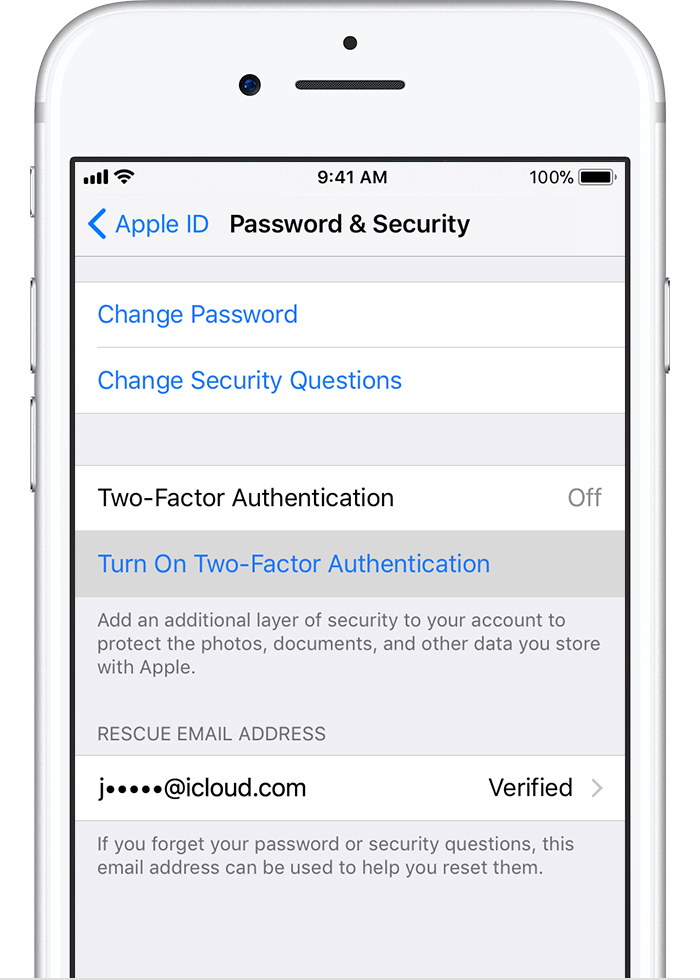 |
| Source: https://support.apple.com/en-ca/HT204915 |
Example 2 - Enabling MFA on GitHub
In GitHub, go to your profile -> security, and click: |
How Secure is your Password?
Speaking of strong passwords, how secure is a 92 bits password compared to my own password? According to howsecureismypassword.net:- your simple password like "Apple123" is broken instantly;
- a complex password as that one generated above would be broken in 52 quadrillion years;
Just access that type and enter your password to get a quick feedback on how long it would take for someone to crack your passwords:
 |
| Source: https://howsecureismypassword.net/ |
Spot the
difference? Few hours x 52 quarillion years. But wait! There are
techniques to speed up this process but we will not cover them now. The
objective of that was to illustrate the importance of creating and using
stronger passwords.
Conclusion
On this post I presented many suggestions on how to create strong passwords, store, transport and additional protection layers such as MFA. Please, start use them all and make your information safer. As a final note, consider using stronger passwords and enabling MFA on all your accounts.
See Also
- My journey to 1 million articles read
- Security and development: how much is being done?
- Security is only as strong as the weakest link
- The Laws of security
- Privacy and Ethics
- Security Boundaries
- Securing our front-end
- Integrated security vulnerability alerts on GitHub - Why it matters
- Dropbox officially debuts its password manager




