It's possible to enable ASP.NET error pages on Azure by using the new Azure Serial Console. Let's see how.
By default, ASP.NET web applications running on a remote server set the customErrors property to "RemoteOnly". That means that, unless you're running on the local server, you won't be able to view the original error and the stack trace related it. And that's a good thing! A lot of successful hacks derive from understanding the exception messages and working around them.But what if you're testing a new server, a new deployment process or just released a new feature and need to enable the error pages very quickly? Well, if you're using Azure, you can use Azure Serial Console to do the job. No SSHing, no RDPing or uploading of configurations to the remote environment. Let's see how.
Azure Serial Console
Today we will use Azure Serial Console. According to Microsoft:The Serial Console in the Azure portal provides access to a text-based console for virtual machines (VMs) and virtual machine scale set instances running either Linux or Windows. This serial connection connects to the ttyS0 or COM1 serial port of the VM or virtual machine scale set instance, providing access independent of the network or operating system state. The serial console can only be accessed by using the Azure portal and is allowed only for those users who have an access role of Contributor or higher to the VM or virtual machine scale set.In other words, Azure Serial Console is a nice, simple and accessible tool that can be run from the Azure portal allowing us to interact with our cloud resources including our Azure App Services.
Accessing the console
To access the console for your web application, first we find our Azure App Service in the Portal by clicking on App Services:Selecting the web site we want to open:
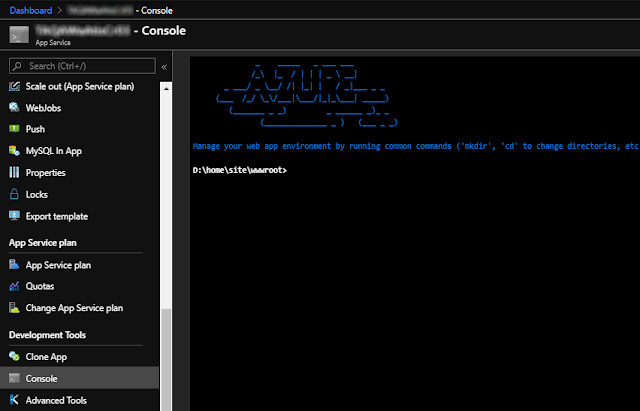
And click on Console on the Development Tools section. You should then see a shell similar to:
Using the Console
Now the fun part. We are ready to interact with our App Service directly from that shell. For starters, let's get some help:The above screenshot shows some of the administrative commands available on the system. Most of them are standard
Linux Tools on Azure Serial Console
Turns out that Redmond is bending to the accessibility, ubiquity and to the power of POSIX / open source tools used and loved by system administrators such as ls, diff, cat, ps, more, less, echo, grep, sed and others. So before jumping to the solution, let's review what we can do with some of these tools. |
| Example 1: a better dir with ls |
 |
| Example 2: Creatting and appending content to files using echo, pipes and cat |
 |
| Example 3: getting disk information with df |
 |
| Example 4: viewing mounted partitions with mount |
 |
| Example 5: Displaying differences between files using diff |
 |
| Example 6: Getting kernel information using uname |
 |
| Example 7: Even curl and scp is available! |
Disabling Custom Errors
Okay, back to our problem. If you know some ASP.NET, you know that the trick is to modify the customErrors Element (ASP.NET Settings Schema) and set the property to Off . So let's see how we can change that configuration using a command line tool.Backing up
Obviously we want to backup our web.config. I hope that's obvious with:
cp web.config web.config.orig
Using sed to replace configuration
Now, we will use sed (a tool available on the GNU operating system that Linux hackers can't live without) to change the setting directly from the console. I'm a sed geek and use it extensively in a Hugo project I've been working on (thousands of markdown files). Together with Go, the i3 window manager, Vim, ranger and grep, my Fedora workstation becomes an ideal development environment. Now, back to .NET...Testing the Patch
We can safely test if our changes will work by typing:
sed 's/RemoteOnly/Off' web.config
Applying the Patch
Let's jump right to how to replace our customErrors element from RemoteOnly to Off ? The solution is this simple one-liner script:
sed -i 's/RemoteOnly/Off/' web.config
Switching Back
Now, obviously we may want to switch back. That's why it was important to backup your web.config before. We can switch back by replacing the changed web.config with the original:
rm web.config
mv web.config.orig web.config
Or by running sed again, this time with the parameters inverted:mv web.config.orig web.config
sed -i 's/Off/RemoteOnly/' web.config
Security Considerations
I hope I don't need to repeat that it's unsafe to leave error pages off on your cloud services. Even if they are simply a playground, there are risks of malicious users pivoting to different services (like your database) and accessing confidential data. Please disable them as soon as possible.What about Kudu?
Yes, Azure Kudu allows editing files on a remote Azure App Service by using a WISIWYG editor. However, we can't count on that always, everywhere. Remember, with the transition to a microservice-based architecture, more and more our apps will run on serverless and containerized environments meaning tools like that wouldn't be available. So the tip presented on this post will definitely stand the test of time! 😉Final Thoughts
Wow, that seems a long post for such a small hack but I felt the need to stress certain things here:- Developers shouldn't be afraid to use the terminal - I see this pattern especially with Microsoft developers assuming that there should always be a button to do something. The more you use the terminal, the more confident you'll be with the tools you're using regardless of where you are.
- Microsoft is moving towards Linux and you should too - The GNU tools prove an unimaginable asset to know. Once you know how to use them better, you'll realize that your toolset grows and you get more creative getting things faster. Plus, the ability to pipe output between them yields unlimited possibilities. Don't know where to start? WSL is the best way to learn the Linux on Windows 10.
- Be creative, use the best tool for the job - choose wise the tool you use. Very frequently the command line is the fastest (and quickest) way to accomplish most of the automatic workflow. And it can be automated!
Conclusion
The Azure Serial Console can be a powerful tool to help you manage, inspect, debug and run quick commands against your Azure App Service and your Virtual Machines. And combined with the Linux tools it becomes even more powerful!And you, what's your favorite hack?
References
- Azure Serial Console
- Microsoft Docs | customErrors Element (ASP.NET Settings Schema)
- Serial Console for Linux VMs
- Serial Console for Windows VMs
- The Basics of Using the Sed Stream Editor to Manipulate Text in Linux
See Also
- Microservices in ASP.NET
- My journey to 1 million articles read
- Adding Application Insights telemetry to your ASP.NET Core website
- Creating ASP.NET Core websites with Docker
- Send emails from ASP.NET Core websites using SendGrid and Azure
- Hosting NuGet packages on GitHub
- Configuration in .NET Core console applications
- How to create a Ubuntu Desktop on Azure
- Building and Running ASP.NET Core apps on Linux
- Windows Subsystem for Linux, the best way to learn Linux on Windows
- How I fell in love with i3
- Why I use Fedora Linux






